
Slack has started sending out emails informing users that their account passwords have been reset due to being compromised during the Slack 2015 security incident. Slack has stated that this is only affecting 1% of their users.
In 2015, Slack was hacked and an unauthorized user was able to gain access to their infrastructure, including a database containing hashed passwords. The attackers also injected a script that would capture passwords in plain text as they were entered by users logging into their workspaces.
"In 2015, unauthorized individuals gained access to some Slack infrastructure, including a database that stored user profile information including usernames and irreversibly encrypted, or “hashed,” passwords. The attackers also inserted code that allowed them to capture plaintext passwords as they were entered by users at the time. "
After the incident, Slack reset the passwords for the users that they could determine were compromised by this incident and encouraged others to reset their passwords as well.
In an a security notice published today, Slack stated they were contacted by a researcher through their bug bounty program about potentially compromised accounts. After investigation it was determined that all of these accounts were active and logged in during their 2015 security incident, which is when they were most likely compromised.
To be safe, Slack has decided to reset the passwords for all accounts that match the following criteria:
- created your account before March 2015,
- AND have not changed your password since,
- AND your account does not require logging in via a single-sign-on (SSO) provider.
Slack states this only affects 1% of their user base and that users logging in via single-sign-on (SSO) are not affected.
For those users who are affected, Slack has started sending out password reset notifications explaining why their passwords have been reset.
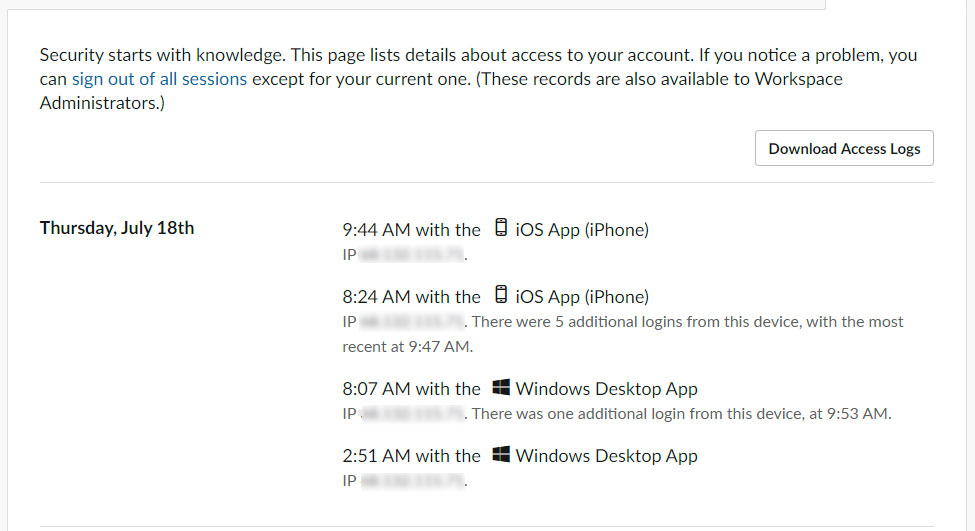
The full text of this notification can be read below:
We were contacted through our bug bounty program by someone with information about potentially compromised Slack credentials, the email addresses and passwords people use to access the service. We investigated and determined the majority of credentials matched accounts that logged in to Slack during the 2015 security incident.
We have no reason to believe your account was affected. However, out of an abundance of caution we've decided to reset all passwords that have not been changed since March of 2015. Your account is included in this group. The affected account is:
For those who receive this email and are concerned that unauthorized users may have accessed their account, you can check your workspace's access logs to see what IP addresses have logged in previously.
Slack also recommends that users enable 2-factor authentication on their accounts to make them more secure.


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now