
The multiple warnings about patching Windows systems against the BlueKeep vulnerability (CVE-2019-0708) have not gone unheeded. Administrators of enterprise networks listened and updated most of the machines affected by the issue.
BlueKeep exists in the Remote Desktop Protocol (RDP) on older Windows releases that are still supported (Windows 7, Windows Server 2008 R2, and Windows Server 2008) as well as on OS versions that reached end-of-life status (Windows XP, Windows Server 2003).
Microsoft disclosed the bug details in mid-May when it also addressed the issue, noting that it can be leveraged to achieve remote code execution (RCE) on a vulnerable system.
The severity is so high — critical score of 9.8 out of 10, wormable, no user interaction required — that Microsoft issued security updates even for Windows versions it no longer supports. For this reason, the company advised users to patch as soon as possible.
Warnings come pouring
Security researchers were quick to test the effects of exploiting BlueKeep, the RCE aspect of it in particular. While most attempts achieved only a denial-of-service reaction, multiple experts created exploit code for RCE and this prompted them to urge admins to patch systems on the network before malicious actors create an exploit and start using it.
At the end of May, more than half of the enterprise machines affected by BlueKeep had the security update installed, announced Raviv Tamir, Group Program Manager, Microsoft Threat Protection.
My dashboard remains bleak as only 57% of exposed machines I see worldwide have patched for CVE-2019-0708. GO PATCH! #MDATP pic.twitter.com/EZ8pRyQXwj
— NotNinjaCat (@RavivTamir) May 30, 2019
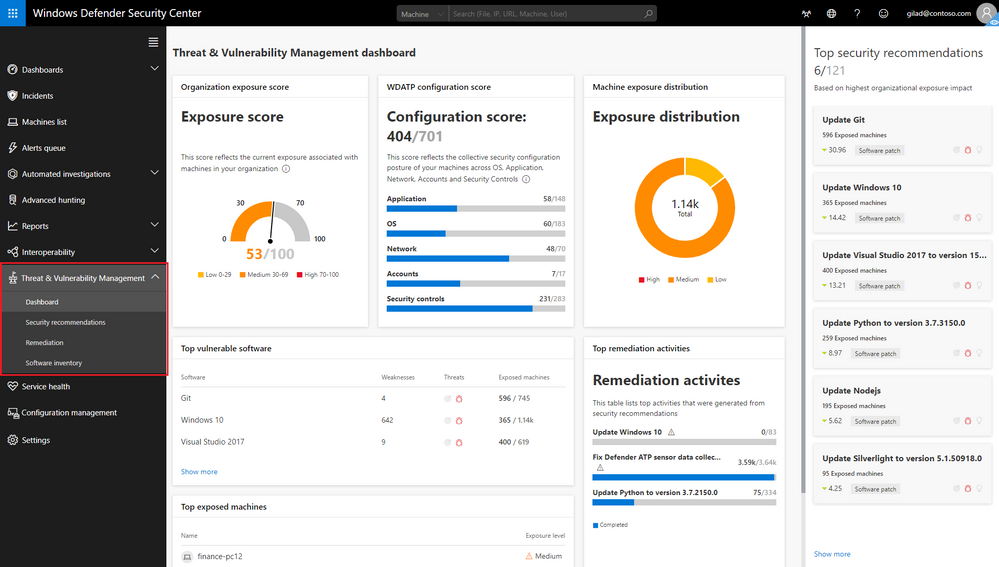
The statistics came from via the Threat & Vulnerability Management in Microsoft Defender ATP - a "platform designed to help enterprise networks prevent, detect, investigate, and respond to advanced threats." It can run on Windows 7 and above and collects data in real time.
A second alert from Microsoft followed, urging users to install the BlueKeep fix and NSA advised for the same precaution on June 4.
The two warnings seem to have given a jolt for patching as the number of systems protected against this flaw increased to 72.4%.
"Numbers are going up - now at 72.4% worldwide. That’s better but still not good enough. KEEP PATCHING! #BlueKeep #MDATP"
On June 17, the Department of Homeland Security's Cybersecurity and Infrastructure Security Agency reiterated the advice, confirming that Windows 2000 systems were also susceptible to BlueKeep attacks.
16% of the hosts are still vulnerable
After all the cautionary notifications, the worldwide update rate against CVE-2019-0708 grew to 83.4%, as Tamir states in a tweet on Thursday.
Another update - worldwide update rate for CVE-2019-0708 numbers are up to 83.4%. KEEEEEEP PATCHING! #BlueKeep #MDATP https://t.co/0xyDebfRes
— NotNinjaCat (@RavivTamir) June 20, 2019
When asked about the number of computers that continue to be vulnerable to BlueKeep, as reported by Microsoft Defender ATP, Tamir told BleepingComputer that there are still several millions of them.
These statistics reflect the reality in enterprise networks, which would be most affected by a BlueKeep outbreak as the vulnerability allows malware to spread from host to host in a similar fashion as WannaCry.


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now